Protectstar Home Page
Shaping Security is more than a slogan to us—it’s our promise.
We develop holistic, human-centered security solutions that just work—independent, transparent, and without unnecessary data collection.
Join our mission and help shape a digital future where
trust and freedom go hand in hand.
Featured in top press worldwide
Your All-in-One
Digital Security
Anti Spy – Protect Yourself from Spyware
-
First certified anti-spyware protection for smartphones
-
Monitor camera access, prevent screen recordings
-
Darknet check: find out if your data is being traded underground
-
App categorization based on permission risk

Downloads
3M+
App rating
4.9 2813 reviews
Language
EN, DE, +15 more
OS
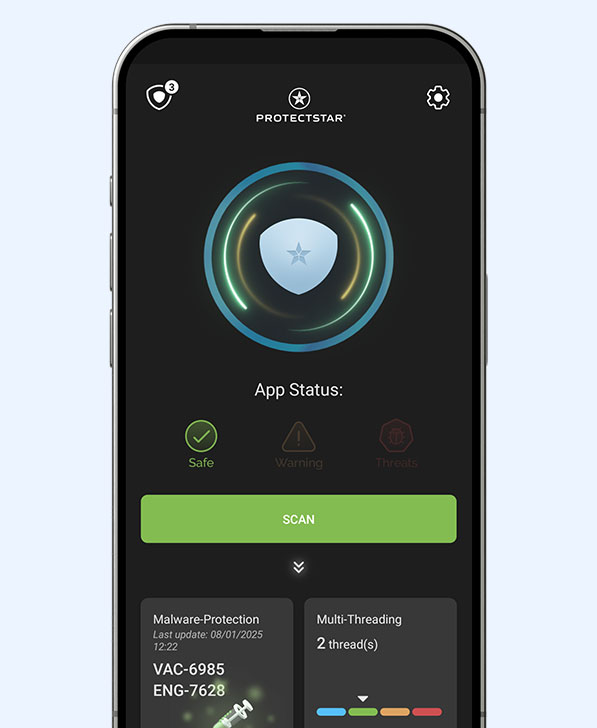
Antivirus AI – Intelligent Protection for Your Android
-
Dual Engine: Traditional scanner + Artificial Intelligence
-
Multiple awards, over 99.9% detection rate
-
Easy to get started, user-friendly interface
-
Cloud-based real-time protection: updated around the clock
Downloads
2M+
App rating
4.8 2828 reviews
Language
EN, DE, +15 more
OS
Perfect Camera Protection with Camera Guard
-
Block Recording: No access without your knowledge
-
Access Log: See who’s attempting to use your camera
-
Whitelist: Allow trusted apps to access your camera

Downloads
500K+
App rating
4.9 433 reviews
Language
EN, DE, +5 more
OS
Take Control of Your Data Traffic with Firewall AI
-
Manage all connections (outbound)
-
Block suspicious services or activities
-
Protection against known spy servers
-
Prevent unauthorized data transmission

Downloads
1M+
App rating
4.8 872 reviews
Language
EN, DE, +16 more
OS
iShredder™ – Permanently and Securely Delete!
-
Permanent data destruction: no recovery possible
-
GDPR-compliant, including a deletion report
-
Simple for private users, powerful for professionals
-
Meets all international data erasure standards

Downloads
1M+
App rating
4.8 597 reviews
Language
EN, DE, +17 more
OS
Don’t Let Anyone Listen In with Micro Guard!
-
Immediate activation: one click is all it takes
-
Alerts for recordings
-
Whitelist for trusted apps
-
Access logs in the protection console

Downloads
500K+
App rating
4.9 493 reviews
Language
EN, DE, +4 more
OS
Multiple Certifications & Awards
by leading testing institutes such as AV-TEST, DEKRA, and Testing Ground Labs
in 2023, 2024, and 2025, and additionally honored with prestigious international awards
including the BIG Innovation Award, AI Excellence Award, and Fortress Cybersecurity Award.
With these achievements, we set new global standards for mobile security and data protection.
-
+99.9%
Detection RateSurpasses even established solutions, detecting threats before they can cause harm.
-
+ Million
AI AlgorithmsDeep Detective™ monitors all processes in real time — adaptive and highly precise.
-
+8 Million
Satisfied UsersIncluding tens of thousands who have successfully neutralized advanced spy apps (APTs).

Delete the file and not just
the association with iShredder!
removes the association with that file.
Why Protectstar?
and even governments.
User-Friendly
Simple, intuitive design so
you’re protected immediately — no expertise required.
No Collection
of User Data
We forego tracking and ad IDs —
your privacy is our top priority.
Energy-Efficient
Enhanced protection without draining
battery or slowing performance.
Artificial Intelligence
Learns with every scan and even detects
newly emerging threats.
Pioneering
Spirit
Read the latest
security and performance tips
Independently Tested:
Anti Spy Android