Erase the drive Windows runs on.
Before Windows starts.
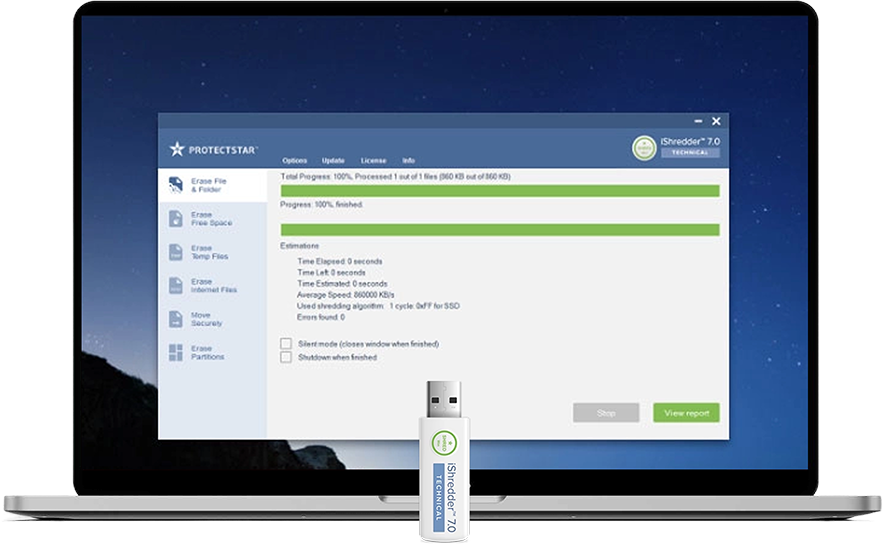
iShredder™ Windows Technical boots from a USB drive and overwrites entire drives, including the Windows system partition, with 23 recognized erasure methods, verification, and a digitally signed report.
- Fortress Cybersecurity Award 2025
- iShredder™ since 2011
- Defense ministries · Government agencies · Forensics
What ordinary deletion leaves behind
More is left behind than you delete.
Windows locks active system areas, swaps memory contents to disk, and automatically saves previous versions. Modern SSDs also contain reserve areas that software can address only to a limited extent. What remains on a drive after deleting files:
Technology with a history
What Technical can do
Six features that work together.
From boot-up to signed report. What sets Technical apart from ordinary erasure software.
Bootable from a USB drive
Outside Windows. System drive included, without the process being blocked by an active operating system.
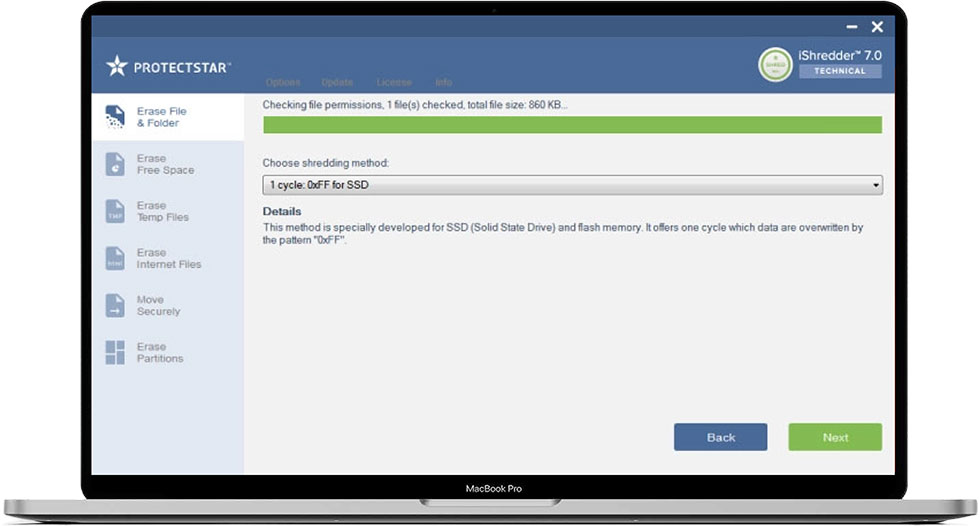
23 recognized erasure methods
From DoD 5220.22-M, NATO, and BSI to Protectstar SDA and ASDA. More methods than any other iShredder edition.
All common storage media
HDD, SSD, USB, SD, CompactFlash, MicroDrive. Via SATA, SAS, SCSI, USB. RAID and NVMe depending on controller.
Signed audit reports
Device ID, method, number of passes, verification result, timestamp, and operator. Digitally signed.
Trace cleanup
Free space, Recycle Bin, pagefile, temporary system files, browser cache, and cookies. Every trace that remains.
Fault tolerance
Defective and locked sectors are detected, documented, and shown in the report. The process continues.
More than TWENTY
secure erasure methods
iShredder™ was developed to effectively meet the data erasure needs of private users and business customers.
To make this possible, the data shredder offers more than twenty secure, patented erasure algorithms certified by government agencies and the military.
Erasure Algorithm:
- 50 Cycles: Protectstar SDA (2007)
- 35 Cycles: Gutmann method
- 8 Cycles: German BSI TL-03423
- 7 Cycles: NATO Standard
- 7 Cycles: DoD 5220.22-M ECE
- 7 Cycles: CANADIAN RCMP TSSIT OPS-II
- 5 Cycles: BSI-2011-VS
- 4 Cycles: Protectstar ASDA (2017)
- 4 Cycles: DoD 5220.22-M E for SSD
- 3 Cycles: Canadian CSEC ITSG-06
- 3 Cycles: HMG Nr. 5 extended
- 3 Cycles: AFSSI-5020
- 3 Cycles: NAVSO P-5239-26 (MFM)
- 3 Cycles: NAVSO P-5239-26 (RLL)
- 3 Cycles: US Army AR380-19
- 3 Cycles: DoD 5220.22-M E
- 3 Cycles: NCSC-TG-025
- 3 Cycles: NIST SP 800-88
- 2 Cycles: RUSSIAN GOST R 50739-95
- 1 Cycle: Australian ISM 6.2.92
- 1 Cycle: 0XFF for SSD
- 1 Cycle: Random Values
- 1 Cycle: NIST SP 800-88 Rev. 1 (2014)
Specifically developed by Protectstar™ Inc. in 2007 it runs through fifty erasure routines.
Data will be overwritten for two times with a random value, afterwards with their complements. It includes the DoD 5220.22-M (E) standard and Peter Gutmann method and random algorithms.
The algorithm from Peter Gutmann was found in 1996 and makes 35 overwrite passes in total.
This algorithm is one of the state-of-the-art methods for data destruction.
In March 2010 the German Federal office for IT Security (BSI) published a new technical BSI Guideline for "Requirements to overwrite memory media".
The method is similar to VSITR standard for magnetic storage media.
In total the new algorithm has 8 cycles, which has to be worked through in chronological order. Includes one cycle of verification.
The NATO method is the deletion standard of North Atlantic Treaty Organization (NATO).
It will overwrite the target data area 7 times.
The first six overwrites are with the fixed values (0x00) and (0xff), alternating between passes.
The 7th overwrite is with a random value i.e. 0x00,0xFF,0x00,0xFF,0x00,0xFF and 7th pass with a random value.
The method for high security is based on the January 1995 'National Industrial Security Program Operating Manual'by the Department of Defense (DoD).
In this seven cycle variation (DoD 5220.22-M ECE), data is first overwritten three times with DoD 5220.22-M (E) Standards, then with a specific random value, and finally once again with DoD 5220.22-M (E).
The Royal Canadian Mounted Police Standard RCMP TSSIT OPS-II overwrites data securely with alternating sequences with a total of seven cycles.
The German Federal office for IT Security (BSI) describes in the technical BSI guideline for 'Requirements to overwrite memory media' from July 2010 the modern method BSI-2011.
This clause includes 5 steps, which is implemented in sequential order.
ASDA enables highly effective, verifiable data erasure with minimal resource consumption. The four passes are designed for efficiency and transparency: read‑after‑write verification and deletion logs document every step. AES‑256 and cryptographically strong random numbers make forensic reconstruction significantly harder. The implementation integrates seamlessly into existing processes.
This method is specially developed for SSD (Solid State Drive) and flash memory, based on the U.S.
Department of Defense's standard DoD 5220.22-M E. It will overwrite data four times.
The Canadian CSEC ITSG-06 sanitization method has three cycles and was published in 2006 by Communication Security Establishment Canada (CSEC).
The HMG Infosec Standard No 5 - enhanced level is approved to wipe UK Government Top Secret data and has also been approved by NATO.
The algorithm is a three pass overwriting algorithm: first pass - with zeros (0), second and third passes with its complement and random values(with last pass verification).
The AFSSI-5020 sanitization method was originally defined in the Air Force System Security Instruction 5020 by the United States Air Force (USAF) in 1996 and may still be today.
This is the US Navy standard NAVSO P-5239-26 for MFM encoded drives.
This deletion method first writes the fixed value (0xffffffff) to the target data area, then the fixed value (0xbfffffff) and then random values.
Finally, the target data area is read to verify the overwrites.
This is the US Navy standard NAVSO P-5239-26 for RLL encoded drives.
This deletion method first writes the fixed value (0xffffffff) to the target data area, then the fixed value (0x27ffffff) and then random values.
Finally, the target data area is read to verify the overwrites.
AR380-19 is the data shredding algorithm specified and published by the U.S. Army.
The algorithm is a three pass overwriting algorithm: first pass - with random bytes, second and third passes with certain bytes and with its complement (with last pass verification).
The method for low security but for high execution speed is based on the January 1995 'National Industry Security Program Operating Manual' from the DoD (US DoD 5220.22-M).
The variation (DoD 5220.22-M E) offers 3 cycles in which the data are overwritten with first a set value, then its complement , and then a random value.
The American NCSC-TG-025 standard of the National Computer Security Center (NCSC) securely overwrites existing information on a data medium three times.
The in 2006 released standard is the Special Publication 800-88 from NIST, which is the go-to data erasure standard for organizations in the United States. Its principles can apply to magnetic, flash-based, and other storage technologies, from USB drives to servers.
The Russian data deletion standard GOST R 50739-95 for secure data erasure overwrites the target data area two times. In the first pass with a zero, and in the second pass with random characters.
ISM 6.2.92 is the Australian government's data sanitization standard.
The method was originally defined in the Information Security Manual (ISM) issued by the Australian Department of Defense: Intelligence & Security.
The ISM 6.2.92 sanitization cannot be used to sanitize classified information.
This method is specially developed for SSD (Solid State Drive) and flash memory.
It offers one cycle which data are overwritten by the pattern "0xFF".
This method for lowest security but for very high execution on speed. It offers only one cycle which data are overwritten with random values.
In December 2014, the guidelines were revised, making the current version “NIST Special Publication 800-88 Rev. 1”.
See here the description of the method you have selected.
Bootable from a USB drive
When the system drive itself must be erased, Technical starts before Windows.
As long as Windows is running, parts of the system partition are locked: pagefile, registry hives, Master File Table, shadow copies. Anyone who wants to verifiably clear a device before decommissioning or disposal has to work outside the running system.
Technical boots from a prepared USB drive into its own minimal environment. No Windows, no open handles, no protected areas — only direct access to supported connected drives.
- Erases the boot drive, including the Windows partition
- Reaches addressable system areas such as the Master File Table, shadow copies, pagefile, and hibernation file
- Works even without an installed operating system
- Direct access to IDE/ATA, SATA, SAS, SCSI, USB, and RAID
23 recognized erasure methods
From DoD to BSI. From 1 to 50 passes.
Choose the standard that matches your compliance requirement: government audit, ISO requirement, defense standard, or internal company policy.
Military & Defense
- NATO Standard7 passes
- DoD 5220.22-M ECE7 passes
- DoD 5220.22-M E for SSD4 passes
- DoD 5220.22-M E3 passes
- US Army AR380-193 passes
- USAF AFSSI-50203 passes
- NAVSO P-5239-26 (MFM)3 passes
- NAVSO P-5239-26 (RLL)3 passes
Government Agencies & Public Sector
- German BSI TL-034238 passes
- BSI-2011-VS5 passes
- NIST SP 800-883 passes
- Canadian RCMP TSSIT OPS-II7 passes
- Canadian CSEC ITSG-063 passes
- HMG Infosec No. 5 extended3 passes
- NCSC-TG-0253 passes
- NIST SP 800-88 Rev. 1 (2014)1 pass
- Russian GOST R 50739-952 passes
- Australian ISM 6.2.921 pass
Protectstar: Proprietary Algorithms
- Protectstar SDA50 passes
- Protectstar ASDA4 passes
Academic & Hardware-Specific
- Gutmann method35 passes
- 0xFF for SSD1 pass
- Random Values1 pass
NIST SP 800-88 Rev. 2 was published by NIST in September 2025 and supersedes Rev. 1. iShredder Technical lists the supported NIST methods according to the procedures implemented in the product.
Award
Fortress Cybersecurity Award 2025 for iShredder™.
An independent jury of experts honored iShredder™ with the 2025 Fortress Cybersecurity Award. The evaluation covered technical innovation, conformity with international security standards, performance, and user guidance.
In this award class: AT&T Dynamic Defense, Lenovo CRaaS, Hitachi Vantara, IBM Cloud Security Hub, 1Password, Norton, SUSE Security.
Read the background on the awardiShredder™ Windows · Edition Comparison
Five editions. One for complete system erasure.
Technical is the only edition with USB boot, all standards, and server compatibility in one package.
| Feature | Professional | Military | Server | Military Server | Recommended Technical |
|---|---|---|---|---|---|
| Securely erase files, folders & partitions | Ja | Ja | Ja | Ja | Ja |
| Securely move files & folders | Ja | Ja | Ja | Ja | Ja |
| Securely erase external drives | Ja | Ja | Ja | Ja | Ja |
| Smart Erasure Assistant | Ja | Ja | Ja | Ja | Ja |
| Signed audit reports | Ja | Ja | Ja | Ja | Ja |
| SSD & flash algorithms | Ja | Ja | Ja | Ja | Ja |
| Advanced military methods (NATO, NAVSO, AFSSI, CSEC) | Nein | Ja | Nein | Ja | Ja |
| Total erasure methods | 11 | 23 | 11 | 23 | 23 |
| Windows Server compatible | Nein | Nein | Ja | Ja | Ja |
| Bootable from a USB drive | Nein | Nein | Nein | Nein | Ja |
System & Boot
What you need before you start.
Technical is delivered as a bootable image. These are the hardware and configuration requirements.
Delivery format
Bootable Image
- Delivered as an ISO file after purchase
- Transfer to a USB drive with common imaging tools such as Rufus or Etcher
- USB drive with at least 2 GB of free space
- No installed Windows required on the target device
Boot environment
UEFI & Classic BIOS
- UEFI and legacy BIOS systems
- Secure Boot is supported depending on device and BIOS configuration
- Set boot order to USB
- Can be used offline, no Internet connection required
Storage media
HDD, SSD, NVMe, USB
- SATA, SAS, SCSI, USB
- NVMe depending on controller and boot environment
- RAID depending on controller, drivers, and configuration
- Defective or locked sectors are documented in the report
For NVMe drives and modern SSDs, we recommend also using a manufacturer-provided hardware Secure Erase if available. Actual sanitization on solid-state media also depends on wear leveling and controller behavior.
GDPR & Audit
Every erasure. Verifiably documented.
In certain cases, the GDPR requires the erasure of personal data (Art. 17) and obligates controllers to demonstrate compliance with the data protection principles (Art. 5). iShredder Technical supports this proof of compliance with digitally signed reports.
- Supports GDPR-compliant documentation. Documents erasure processes under Art. 17 (right to erasure) and Art. 5 (accountability) with method, storage medium, result, timestamp, and operator.
- Audit support. Reports can support internal audits, ISO 27001 processes, privacy reviews, and government procedures.
- Digitally signed. Subsequent changes to the report become detectable.
What the erasure report contains
Every report contains the fields required for an audit:
- Device ID
- Serial number
- Windows version
- Method
- Number of passes
- Verification
- Timestamp
- Operator
Important notice before you start
iShredder Technical is designed for final erasure processes. Carefully check the target medium, existing backups, and selected method before starting the process. Erased data cannot be recovered.
Licenses & Care Plan
One edition. License options in the shop.
iShredder™ Windows Technical
The complete edition. Bootable from a USB drive, all 23 methods, Windows Server support — everything included.
View current license options, term, and Care Plan in the shop
- 23 recognized erasure methods
- Bootable from a USB drive
- Windows 10, Windows 11 & Windows Server environments
- Signed audit reports
- SSD, RAID, USB & server support
- Advanced military methods (NATO, NAVSO, AFSSI, CSEC)
3 Years Premium Support
Extend your license with 36 months of premium service and free upgrades to all new versions.
Available as an add-on at purchase · Best value
- Premium technical support
- 3 years of free updates & upgrades
- Prioritized handling of requests
- Direct contact with the Protectstar team
Frequently Asked Questions
What you should know before you buy.
When you want to erase the drive that contains your operating system itself — for example before device decommissioning, disposal, re-imaging, or a forensic wipe. As long as Windows is running, the system partition is locked. Only Technical boots from a USB drive outside the system and can also verifiably overwrite the Windows system partition.
If you also need to erase Windows Server systems and require all military standards, Technical is also the only edition that combines everything in one license.
Technical includes methods for SSDs and flash media and overwrites the addressable areas of the drive. With modern SSDs and NVMe drives, complete sanitization also depends on the controller, TRIM, wear leveling, and manufacturer-specific functions. For particularly stringent security requirements, we recommend also checking whether the manufacturer provides a controller-based Secure Erase or Crypto Erase process.
For newer NVMe drives, we also recommend a controller-based hardware Secure Erase if the manufacturer offers one.
After purchase, you receive an ISO file. Write it to a USB drive with any common imaging tool, such as Rufus or Etcher. In the BIOS or UEFI of your device, select the USB drive as the boot medium. Depending on the USB drive, the entire process takes one to two minutes.
The reports are digitally signed and document the device ID, serial number, method, number of passes, verification result, timestamp, and operator. This allows them to support internal audits, privacy reviews, ISO 27001 processes, and technical evidence requirements.
Whether a report is admitted as evidence in a specific court proceeding is decided by the respective court. The reports provide all technically relevant fields for that purpose.
Technical includes built-in strategies for defective, locked, and faulty sectors. The process continues, faulty areas are logged in the report and marked with the sector address. At the end, you know exactly what was fully overwritten and what was not.
IDE/ATA, SATA, SCSI, SAS, USB, and hardware or software RAID arrays. This covers HDDs, SSDs, NVMe drives, USB flash drives, CompactFlash, SD/microSD, MMC, xD, and MicroDrive — from consumer to enterprise hardware in a single solution.
For Audits, IT, and Forensics
When a device is retired, the proof remains.
iShredder™ Windows Technical starts from USB, overwrites entire drives, and creates signed reports for audits, privacy teams, and technical evidence.
 English
English Deutsch
Deutsch Español
Español Français
Français Italiano
Italiano Português
Português Русский
Русский العربية
العربية हिन्दी
हिन्दी 日本語
日本語 简体中文
简体中文